ISMS open source challenges
There are many challenges in building an open source ISMS. Find out what these are and how to handle them
Implementing and maintaining an Information Security Management System (ISMS) is a significant investment that is regularly underestimated by organizations. The average cost of obtaining and maintaining an ISMS can range from tens to hundreds of thousands of dollars, depending on the size and complexity of the organization. Industry reports consistently highlight that a substantial portion of this cost is attributed to personnel, consulting fees, and audit expenses. With these costs in mind, small and medium-sized firms naturally explore open-source alternatives, seeking a more budget-friendly approach to achieving ISO 27001 compliance.
The perceived benefits of developing an ISMS using open-source solutions are normally quite clear and intuitive: you immediately save costs through the availability of free policies and documents. Secondly, you accelerate policy writing with out-of-the-box templates. Finally, by using ready-made materials, you can accurately map ISO 27001 from the start. These advantages offer a shortcut to certification, but the reality is slightly more nuanced.
The obvious challenges
While open-source ISMS solutions offer initial cost advantages, they present several challenges that can quickly escalate expenses and effort. Maintaining and improving an ISMS is an ongoing process, requiring continuous investment. Platform costs for hosting and managing the ISMS, salary expenses for dedicated resources, and audit fees quickly accumulate. A certified ISO 27001 lead implementer in Europe, for example, can easily command an annual salary exceeding 60K EUR, excluding social security costs.
Collateral costs should also be anticipated, such as the time and salary costs spent on internal and external audits to maintain the certification plus ISMS maintenance activities such as access reviews, asset reviews, log auditing, security awareness campaign management etc.
Moreover, open-source policies, while readily available, often require extensive customization to align with a company’s operating environment. For instance, policies designed for traditional enterprise networks, with on-premise servers and domain-joined workstations, would not be suitable for cloud-first SaaS companies, which rely heavily on cloud services and remote access. While chatbots can accelerate the initial policy creation process, expert GRC professionals are essential for ensuring accuracy and relevance. Chatbots, while faster and more efficient at writing policies, can produce generic outputs that lack the specificity required for an ISMS implementation that can withstand auditor scrutiny.
Finally, an open-source ISMS is a starting point, not a static solution. Continuous adaptation is necessary to keep pace with evolving ISO standards, technological advancements, and company changes. The ISO 27001 standard is periodically updated, requiring organizations to revise their ISMS to maintain compliance. Without dedicated resources or tools, staying current can become a significant challenge.
The hidden challenges
Beyond the obvious, hidden challenges can significantly impact ISMS implementation and maintenance, often catching organizations unprepared. Initially, firms might gravitate towards tools like verinice. However, these solutions typically necessitate self-hosting, introducing complex installation and ongoing maintenance overhead that translates directly into increased time and salary expenses. This complexity can become problematic when the core objective is only to manage policy documentation. Looking ahead, as the ISMS matures and expands, manual maintenance becomes unsustainable. Companies exceeding 200 employees often find themselves compelled to adopt specialized GRC platforms, such as DRATA or Vanta, to automate processes and embrace a GRC engineering approach. These platforms, while essential for scalability and efficiency, typically incur annual costs of around USD 50K, excluding potential discounts.
Effort-wise, handling customer security questionnaires can consume a significant portion of a security team’s time. Securing ISO 27001 certification often stems from a need to increase customer trust and meet stringent client security requirements. However, teams frequently fail to account for the influx of information security questionnaires from customers and prospects, which tend to compound over time. These questionnaires, particularly those originating from sectors like financial services, demand substantial time and effort to complete. To illustrate, a mid-sized SaaS company with 200 employees and 400 clients can expect to handle at least two questionnaires weekly. Without automation, a team might spend an average of five hours per questionnaire, translating to approximately 520 hours annually. Given a standard work year of 2,080 hours, this equates to over 25% of the team’s time dedicated solely to questionnaire responses. A huge investment of time.
Impact-wise, maintaining management engagement is crucial for the long-term success of the ISMS. Initially, management may be enthusiastic about achieving ISO 27001 certification. However, the long-term challenge lies in sustaining management engagement beyond the initial phase. While the certification will retain its importance as a customer acquisition and retention tool, the perceived value of the underlying ISMS can diminish, particularly as operational costs rise. The critical task is to continually demonstrate the ISMS’s strategic importance, preventing it from being viewed as a compliance burden. If management perceives the ISMS as a purely administrative, cost-intensive exercise, securing necessary funding and executive sponsorship for ongoing program enhancements will become harder over time. Therefore, it is imperative to consistently reinforce the ISMS’s role in safeguarding customer trust and directly contributing to the company’s bottom line.
Efficiently overcoming challenges
These challenges are manageable with proactive planning and strategic resource allocation. For short-term cost management, there are two clear approaches. If your team includes a GRC expert, resist using open-source software, prioritizing simplicity to minimize maintenance overhead. Instead, leverage chatbots for initial policy drafting and utilize a wiki platform for centralized storage.
Focus time and resources on customizing the ISMS to your specific operational needs, and allocate any remaining funds to a basic security training platform such as safetitan, costing roughly USD 3K annually for a 150-200 employee company. Conversely, if your team lacks in-house GRC expertise, engage an external consultant or firm for ISMS implementation and certification. While this approach carries a higher upfront cost (approximately USD 50-60K), it significantly reduces the time and labour expenses associated with an untrained internal team. In the long term, strategically transition towards a specialist GRC platform, aiming to automate processes and reduce ongoing maintenance costs.
Then, develop an efficient questionnaire handling process by employing three key strategies. Firstly, establish a collaborative process between your security team and customer success management (CSM) or sales. Customer-facing teams should assume primary responsibility for receiving, reviewing, and pre-filling questionnaires, as well as distributing unresolved questions to subject matter experts (SMEs). This allows the security team to focus on core security functions, providing input only when necessary. Secondly, create a centralized database of questionnaire answers, jointly managed by security and CSM/sales. This knowledge base will empower CSM/sales to handle security-related inquiries independently. Thirdly, after procuring a GRC platform, integrate a questionnaire-handling AI tool. Utilize the existing database of answers to train the AI, enabling automated and accurate responses.
To maintain management engagement, adopt lean management reporting practices. Focus on concise, data-driven reports that highlight the business value of security initiatives. By involving the right stakeholders, providing proper briefings, and empowering decision-making, you’ll secure stronger agility and alignment between business and security leadership.
What to do with a limited budget
Even with limited budgets, a robust ISMS is achievable. For policy drafting, use free resources and AI tools like ChatGPT.
To optimize expenses during the certification process, teams can limit the ISMS scope to essential products and services. This focused approach minimizes the complexity and resources required by focusing on minimal implementation requirements such as core and basic control policies. A SaaS company, for example, may tailor its certification scope to target its software products, thereby avoiding the costs associated with covering wider company IT assets (e.g. laptops, finance systems, etc.)
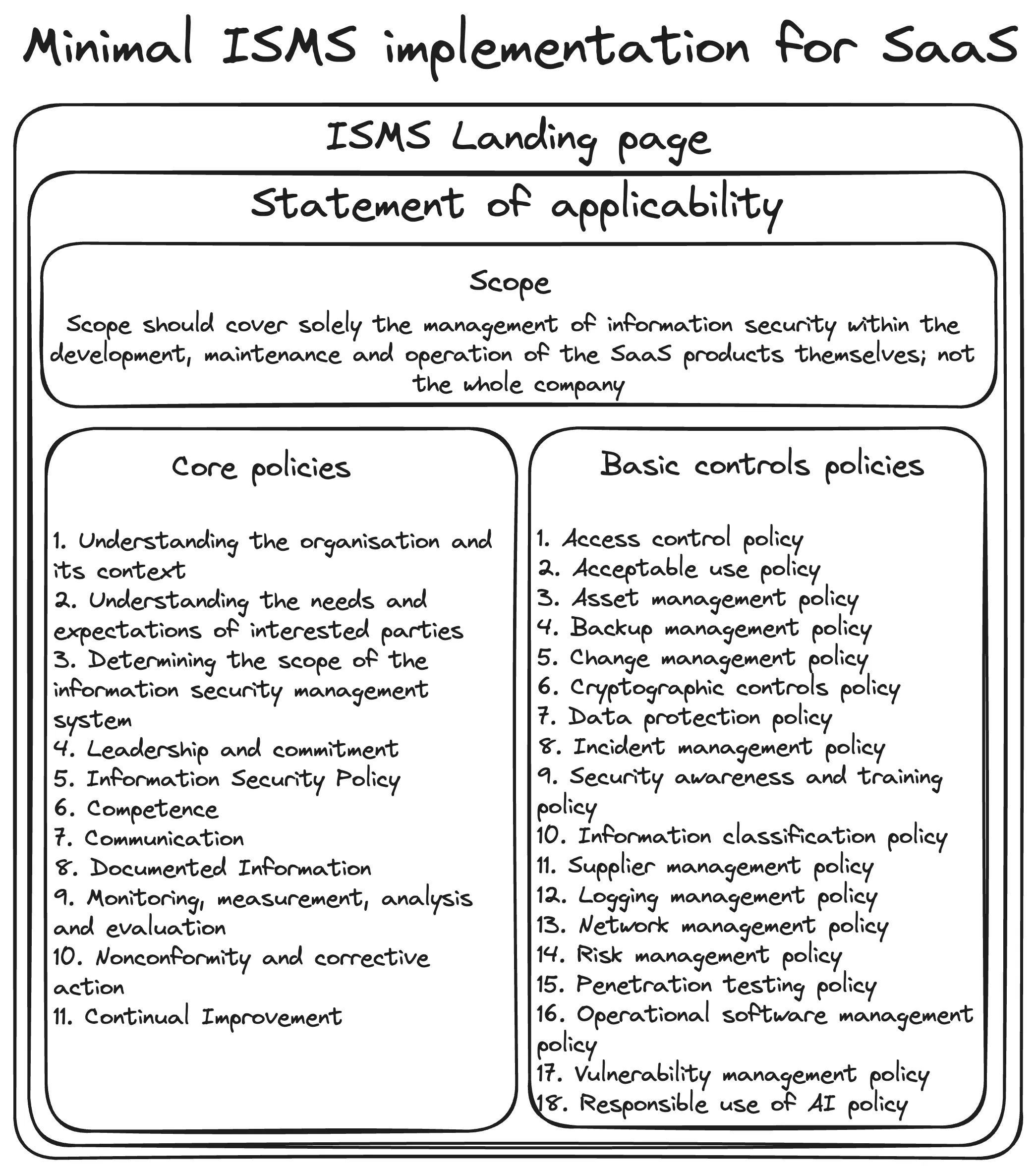
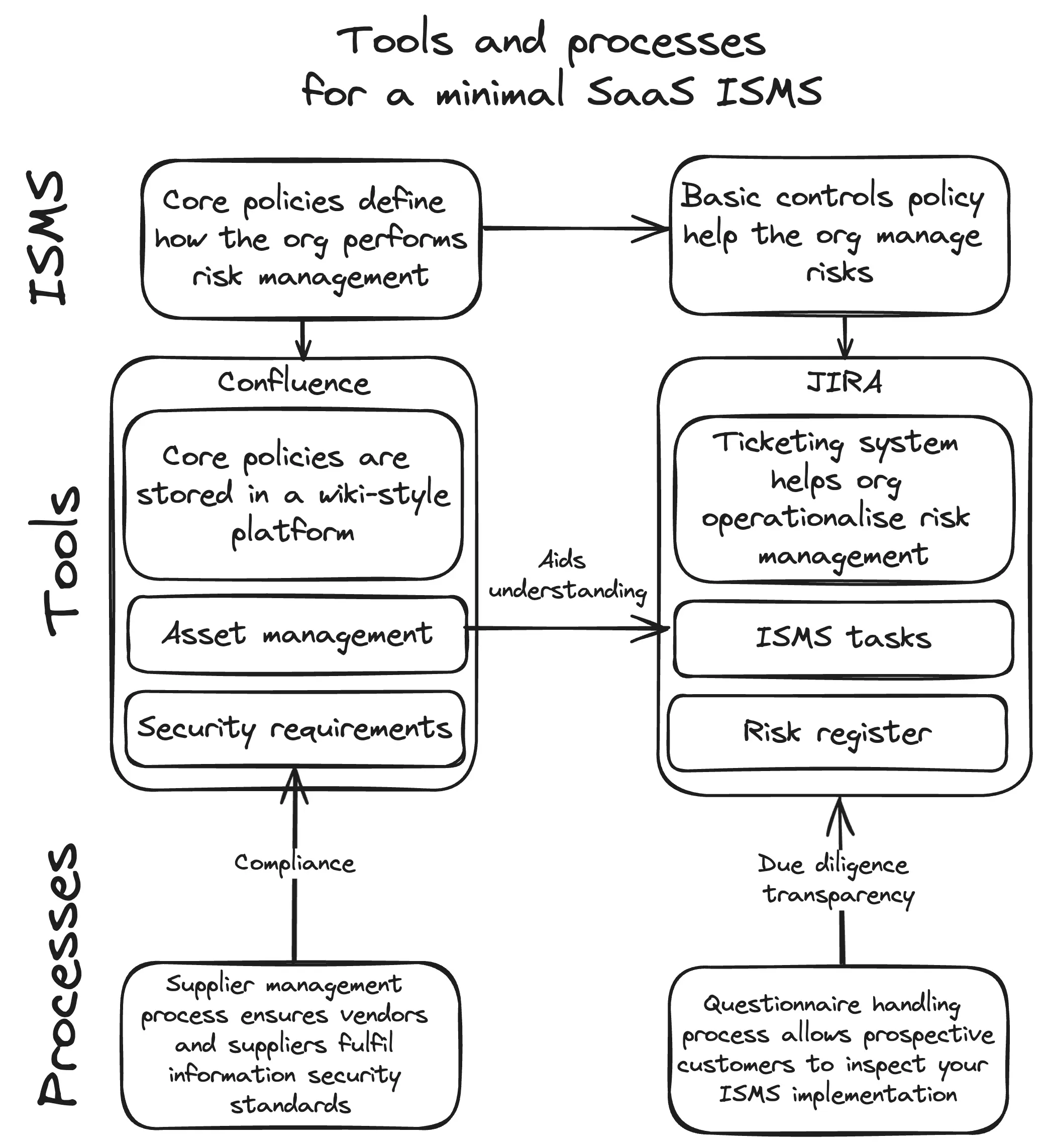
Secondly, focus on essential tools and processes to save costs and build the operational processes to support the ISMS. At a minimum, companies should source software for document content storage, with platforms like Atlassian Confluence being ideal, though even storing policies on shared drives suffices as long as access is controlled. Then, a ticketing system like Atlassian JIRA is needed to operationalize the ISMS by enabling recurring tasks and integrating plugins such as Risk Register for JIRA. Also, develop an asset management process, which is crucial for certification. Deploy most of the budget on a basic device management solution to build an initial inventory of assets. Then, avoid buying specialized asset management software and stick to Excel-based solution. Finally, develop a supplier management process to ensure vendors align with security standards. Use AI chatbots to run risk assessments initially. The picture below gives a good overview of the tools and processes needed for a minimal ISMS. Its SaaS-specific but can be easily adapted to any company looking to build an ISMS:
However, certain investments are unavoidable. Plan to allocate budget for dedicated personnel to manage the ISMS and coordinate with external auditors. Include the costs of external certification audits and ongoing compliance activities. By focusing on essential tools and processes, lean security teams can save substaintial costs when building the initial processes and infrastructure to support the ISMS.
Conclusion
While open-source ISMS solutions may appear to offer a cost-effective shortcut, they come with hidden challenges that require careful handling. A balanced approach, combining cost-effective strategies with strategic investments, is essential for successful and sustainable ISMS implementation. Organizations must recognize that an ISMS is not a one-time project but an ongoing commitment. By focusing on efficient processes, leveraging AI, and maintaining management engagement, organizations can navigate the complexities of ISMS-building and ensure long-term security and compliance, ultimately protecting customer trust and driving business success.
